Federal authorities have arrested and indicted a 20-year-old U.S. Military soldier on suspicion of being Kiberphant0m, a cybercriminal who has been promoting and leaking delicate buyer name data stolen earlier this 12 months from AT&T and Verizon. As first reported by KrebsOnSecurity final month, the accused is a communications specialist who was lately stationed in South Korea.

One in all a number of selfies on the Fb web page of Cameron Wagenius.
Cameron John Wagenius was arrested close to the Military base in Fort Hood, Texas on Dec. 20, after being indicted on two felony counts of illegal switch of confidential cellphone data.
The sparse, two-page indictment (PDF) doesn’t reference particular victims or hacking exercise, nor does it embrace any private particulars concerning the accused. However a dialog with Wagenius’ mom — Minnesota native Alicia Roen — crammed within the gaps.
Roen stated that previous to her son’s arrest he’d acknowledged being related to Connor Riley Moucka, a.ok.a. “Judische,” a prolific cybercriminal from Canada who was arrested in late October for stealing information from and extorting dozens of corporations that saved information on the cloud service Snowflake.
In an interview with KrebsOnSecurity, Judische stated he had little interest in promoting the information he’d stolen from Snowflake clients and telecom suppliers, and that he most popular to outsource that to Kiberphant0m and others. In the meantime, Kiberphant0m claimed in posts on Telegram that he was chargeable for hacking into not less than 15 telecommunications corporations, together with AT&T and Verizon.
On November 26, KrebsOnSecurity revealed a narrative that adopted a path of clues left behind by Kiberphantom indicating he was a U.S. Military soldier stationed in South Korea.
Ms. Roen stated Cameron labored on radio indicators and community communications at an Military base in South Korea for the previous two years, returning to america periodically. She stated Cameron was all the time good with computer systems, however that she had no thought he may need been concerned in felony hacking.
“I by no means was conscious he was into hacking,” Roen stated. “It was undoubtedly a shock to me after we discovered these items out.”
Ms. Roen stated Cameron joined the Military as quickly as he was of age, following in his older brother’s footsteps.
“He and his brother after they had been like 6 and seven years outdated would ask for MREs from different international locations,” she recalled, referring to military-issued “meals able to eat” meals rations. “They each all the time needed to be within the Military. I’m unsure the place issues went incorrect.”
Instantly after information broke of Moucka’s arrest, Kiberphant0m posted on the hacker neighborhood BreachForums what they claimed had been the AT&T name logs for President-elect Donald J. Trump and for Vice President Kamala Harris.
“Within the occasion you don’t attain out to us @ATNT all presidential authorities name logs might be leaked,” Kiberphant0m threatened, signing their publish with a number of “#FREEWAIFU” tags. “You don’t assume we don’t have plans within the occasion of an arrest? Assume once more.”
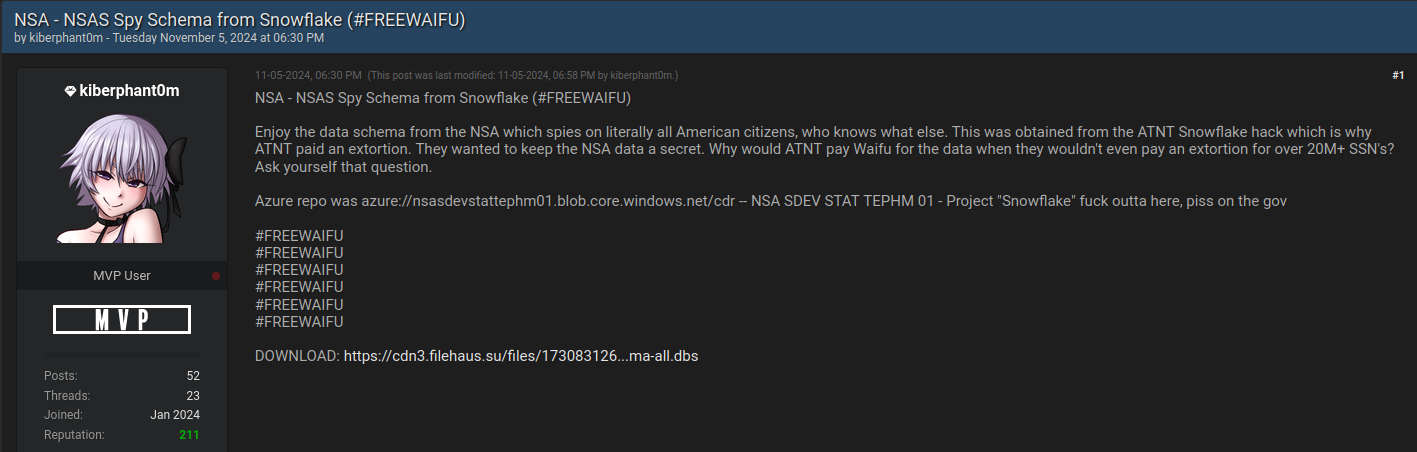
Kiberphant0m posting what he claimed was a “information schema” stolen from the NSA through AT&T.
On that very same day, Kiberphant0m posted what they claimed was the “information schema” from the U.S. Nationwide Safety Company.
On Nov. 5, Kiberphant0m supplied name logs stolen from Verizon’s push-to-talk (PTT) clients — primarily U.S. authorities businesses and emergency first responders. On Nov. 9, Kiberphant0m posted a gross sales thread on BreachForums providing a “SIM-swapping” service focusing on Verizon PTT clients. In a SIM-swap, fraudsters use credentials which might be phished or stolen from cell phone firm staff to divert a goal’s cellphone calls and textual content messages to a tool they management.
The profile photograph on Wagenius’ Fb web page was deleted inside hours of my Nov. 26 story figuring out Kiberphant0m as a probable U.S. Military soldier. Nonetheless, a lot of his unique profile photographs stay, together with a number of that present Wagenius in uniform whereas holding varied Military-issued weapons.
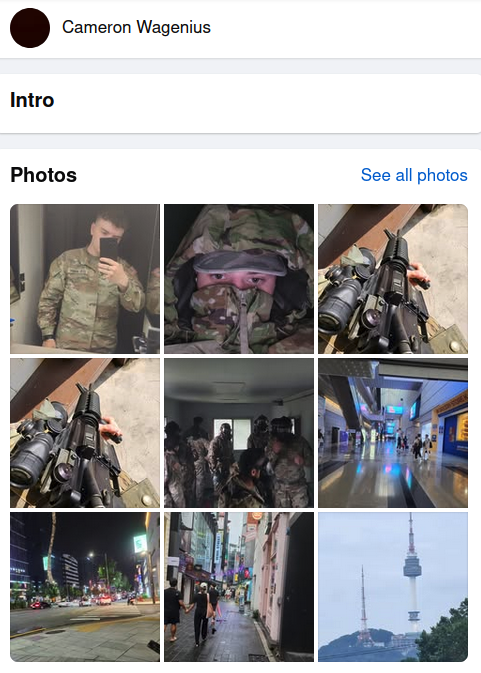
A number of profile photographs seen on the Fb web page of Cameron Wagenius.
November’s story on Kiberphant0m cited his personal Telegram messages saying he maintained a big botnet that was used for distributed denial-of-service (DDoS) assaults to knock web sites, customers and networks offline. In 2023, Kiberphant0m offered distant entry credentials for a significant U.S. protection contractor.
Allison Nixon, chief analysis officer on the New York-based cybersecurity agency Unit 221B, helped monitor down Kiberphant0m’s actual life identification. Nixon was amongst a number of safety researchers who confronted harassment and particular threats of violence from Judische and his associates.
“Anonymously extorting the President and VP as a member of the navy is a foul thought, nevertheless it’s a good worse thought to harass individuals who specialise in de-anonymizing cybercriminals,” Nixon informed KrebsOnSecurity. She stated the investigation into Kiberphant0m reveals that regulation enforcement is getting higher and quicker at going after cybercriminals — particularly those that are literally residing in america.
“Between after we, and an nameless colleague, discovered his opsec mistake on November tenth to his final Telegram exercise on December 6, regulation enforcement set the pace report for the quickest turnaround time for an American federal cyber case that I’ve witnessed in my profession,” she stated.
Nixon requested to share a message for all the opposite Kiberphant0ms on the market who assume they will’t be discovered and arrested.
“I do know that younger individuals concerned in cybercrime will learn these articles,” Nixon stated. “That you must cease doing silly shit and get a lawyer. Regulation enforcement needs to place all of you in jail for a very long time.”
The indictment in opposition to Wagenius was filed in Texas, however the case has been transferred to the U.S. District Courtroom for the Western District of Washington in Seattle.


