At Databricks, we all know that information is one in every of your most dear property. Our product and safety groups work collectively to ship an enterprise-grade Knowledge Intelligence Platform that lets you defend towards safety dangers and meet your compliance obligations. Over the previous yr, we’re proud to have delivered new capabilities and assets resembling securing information entry with Azure Personal Hyperlink for Databricks SQL Serverless, holding information personal with Azure firewall help for Workspace storage, defending information in-use with Azure confidential computing, attaining FedRAMP Excessive Company ATO on AWS GovCloud, publishing the Databricks AI Safety Framework, and sharing particulars on our strategy to Accountable AI.
In keeping with the 2024 Verizon Knowledge Breach Investigations Report, the variety of information breaches has elevated by 30% since final yr. We imagine it’s essential so that you can perceive and appropriately make the most of our safety features and undertake advisable safety greatest practices to mitigate information breach dangers successfully.
On this weblog, we’ll clarify how one can leverage a few of our platform’s high controls and lately launched safety features to ascertain a sturdy defense-in-depth posture that protects your information and AI property. We may even present an summary of our safety greatest practices assets so that you can rise up and operating rapidly.
Defend your information and AI workloads throughout the Databricks Knowledge Intelligence Platform
The Databricks Platform offers safety guardrails to defend towards account takeover and information exfiltration dangers at every entry level. Within the under picture, we define a typical lakehouse structure on Databricks with 3 surfaces to safe:
- Your shoppers, customers and purposes, connecting to Databricks
- Your workloads connecting to Databricks companies (APIs)
- Your information being accessed out of your Databricks workloads
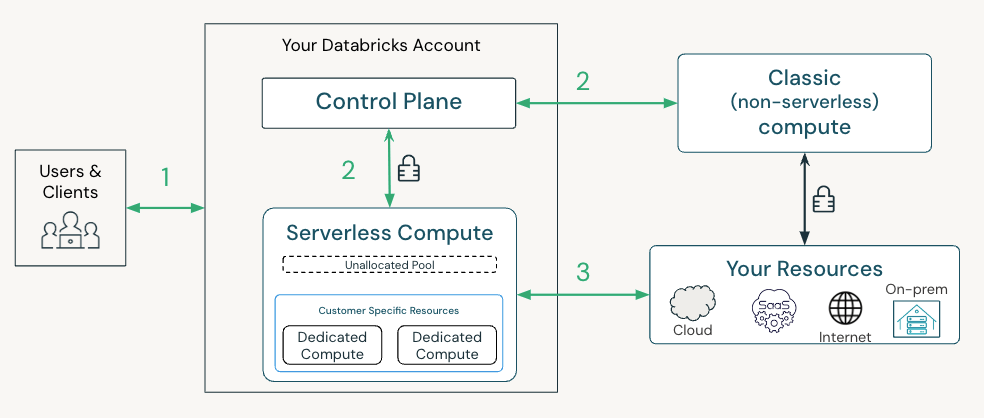
Let’s now stroll by at a excessive stage among the high controls—both enabled by default or obtainable so that you can activate—and new safety capabilities for every connection level. Our full record of suggestions primarily based on completely different menace fashions may be present in our safety greatest observe guides.
Connecting customers and purposes into Databricks (1)
To guard towards access-related dangers, it’s best to use a number of elements for each authentication and authorization of customers and purposes into Databricks. Utilizing solely passwords is insufficient as a consequence of their susceptibility to theft, phishing, and weak person administration. In truth, as of July 10, 2024, Databricks-managed passwords reached the end-of-life and are now not supported within the UI or by way of API authentication. Past this extra default safety, we advise you to implement the under controls:
- Authenticate by way of single-sign-on on the account stage for all person entry (AWS, SSO is robotically enabled on Azure/GCP)
- Leverage multi-factor authentication supplied by your IDP to confirm all customers and purposes which are accessing Databricks (AWS, Azure, GCP)
- Allow unified login for all workspaces utilizing a single account-level SSO and configure SSO Emergency entry with MFA for streamlined and safe entry administration (AWS, Databricks integrates with built-in id suppliers on Azure/GCP)
- Use front-end personal hyperlink on workspaces to limit entry to trusted personal networks (AWS, Azure, GCP)
- Configure IP entry lists on workspaces and in your account to solely enable entry from trusted community places, resembling your company community (AWS, Azure, GCP)
Connecting your workloads to Databricks companies (2)
To forestall workload impersonation, Databricks authenticates workloads with a number of credentials in the course of the lifecycle of the cluster. Our suggestions and obtainable controls rely in your deployment structure. At a excessive stage:
- For Basic clusters that run in your community, we advocate configuring a back-end personal hyperlink between the compute airplane and the management airplane. Configuring the back-end personal hyperlink ensures that your cluster can solely be authenticated over that devoted and personal channel.
- For Serverless, Databricks robotically offers a defense-in-depth safety posture on our platform utilizing a mix of application-level credentials, mTLS shopper certificates and personal hyperlinks to mitigate towards Workspace impersonation dangers.
Connecting from Databricks to your storage and information sources (3)
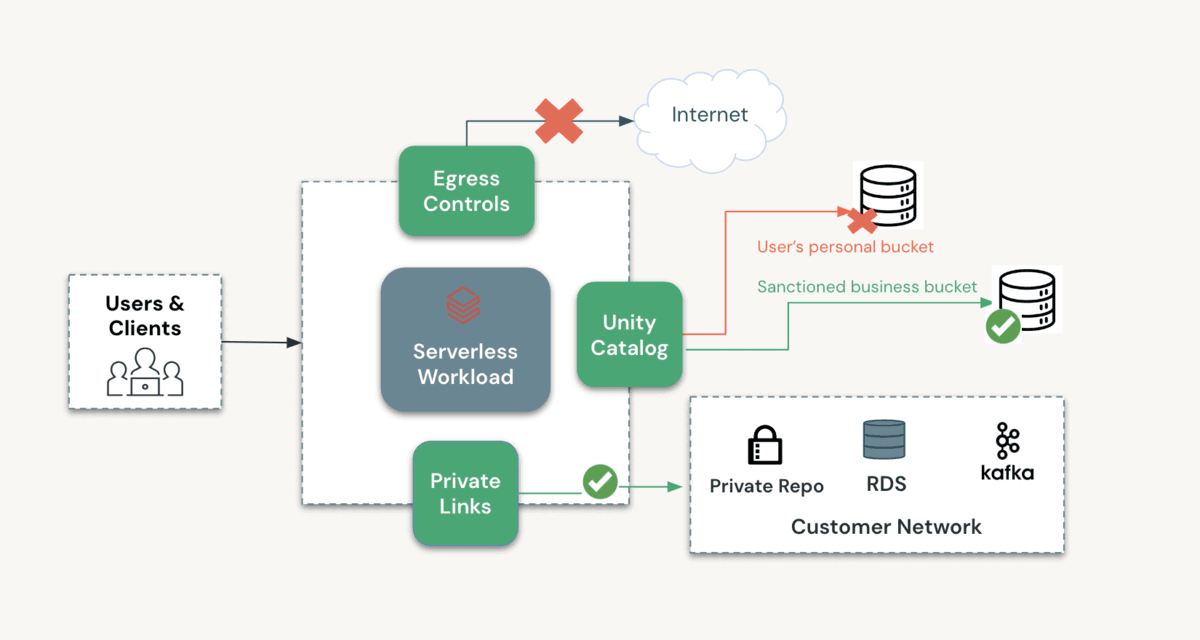
To make sure that information can solely be accessed by the appropriate person and workload on the appropriate Workspace, and that workloads can solely write to approved storage places, we advocate leveraging the next options:
- Utilizing Unity Catalog to control entry to information: Unity Catalog offers a number of layers of safety, together with fine-grained entry controls and time-bound down-scoped credentials which are solely accessible to trusted code by default.
- Leverage Mosaic AI Gateway: Now in Public Preview, Mosaic AI Gateway means that you can monitor and management the utilization of each exterior fashions and fashions hosted on Databricks throughout your enterprise.
- Configuring entry from approved networks: You’ll be able to configure entry insurance policies utilizing S3 bucket insurance policies on AWS, Azure storage firewall and VPC Service Controls on GCP.
- With Basic clusters, you possibly can lock down entry to your community by way of the above-listed controls.
- With Serverless, you possibly can lock down entry to the Serverless community (AWS, Azure) or to a devoted personal endpoint on Azure. On Azure, now you can allow the storage firewall in your Workspace storage (DBFS root) account.
- Sources exterior to Databricks, resembling exterior fashions or storage accounts, may be configured with devoted and personal connectivity. Here’s a deployment information for accessing Azure OpenAI, one in every of our most requested eventualities.
- Configuring egress controls to stop entry to unauthorized storage places: With Basic clusters, you possibly can configure egress controls in your community. With SQL Serverless, Databricks doesn’t enable web entry from untrusted code resembling Python UDFs. To learn the way we’re enhancing egress controls as you undertake extra Serverless merchandise, please this type to hitch our previews.
The diagram under outlines how one can configure a personal and safe atmosphere for processing your information as you undertake Databricks Serverless merchandise. As described above, a number of layers of safety can shield all entry to and from this atmosphere.
Outline, deploy and monitor your information and AI workloads with industry-leading safety greatest practices
Now that we now have outlined a set of key controls obtainable to you, you most likely are questioning how one can rapidly operationalize them for your small business. Our Databricks Safety staff recommends taking a “outline, deploy, and monitor” strategy utilizing the assets they’ve developed from their expertise working with lots of of shoppers.
- Outline: You need to configure your Databricks atmosphere by reviewing our greatest practices together with the dangers particular to your group. We have crafted complete greatest observe guides for Databricks deployments on all three main clouds. These paperwork provide a guidelines of safety practices, menace fashions, and patterns distilled from our enterprise engagements.
- Deploy: Terraform templates make deploying safe Databricks workspaces simple. You’ll be able to programmatically deploy workspaces and the required cloud infrastructure utilizing the official Databricks Terraform supplier. These unified Terraform templates are preconfigured with hardened safety settings much like these utilized by our most security-conscious prospects. View our GitHub to get began on AWS, Azure, and GCP.
- Monitor: The Safety Evaluation Software (SAT) can be utilized to watch adherence to safety greatest practices in Databricks workspaces on an ongoing foundation. We lately upgraded the SAT to streamline setup and improve checks, aligning them with the Databricks AI Safety Framework (DASF) for improved protection of AI safety dangers.
Keep forward in information and AI safety
The Databricks Knowledge Intelligence Platform offers an enterprise-grade defense-in-depth strategy for shielding information and AI property. For suggestions on mitigating safety dangers, please consult with our safety greatest practices guides in your chosen cloud(s). For a summarized guidelines of controls associated to unauthorized entry, please consult with this doc.
We constantly improve our platform primarily based in your suggestions, evolving {industry} requirements, and rising safety threats to higher meet your wants and keep forward of potential dangers. To remain knowledgeable, bookmark our Safety and Belief weblog, head over to our YouTube channel, and go to the Databricks Safety and Belief Heart.


