There are extra vulnerabilities round than ever. The Verizon Knowledge Breach Investigations Report highlighted an virtually 200% development within the exploitation of vulnerabilities in 2023. Within the first seven months of 2024, new vulnerabilities rose by one other 30% in comparison with the earlier 12 months. No surprise vulnerability administration instruments have gotten a staple of the enterprise cybersecurity arsenal.
“Vulnerability administration is a core operate of cybersecurity,” mentioned Michelle Abraham, analysis director, Safety and Belief at IDC. “Leaving vulnerabilities with out motion exposes organizations to limitless threat since vulnerabilities might depart the information however not the minds of attackers.”
Prime vulnerability administration instruments comparability
Many vulnerability administration instruments have comparable options. However once I appeared into them extra carefully, I observed that they every have their very own focus or method. Some are extra specialised than others. I in contrast them based mostly on worth in addition to 4 key options:
- Cloud, on-prem, or each.
- Being a part of a complete cybersecurity suite.
- Automated discovery.
- Automated remediation.
Bear in mind, nevertheless, that an apples-to-apples comparability based mostly on worth is unimaginable because of the other ways distributors worth their services and products in addition to an absence of transparency on pricing.
| Beginning worth | Cloud or on-prem | Cybersecurity suite options | Automated discovery | Automated remediation | |
|---|---|---|---|---|---|
| Tenable | About $4,000 per 12 months for 100 belongings. | Cloud-based. There’s a separate on-prem suite referred to as Tenable Safety Middle that features vulnerability administration. | Vulnerability administration, internet software scanning, cloud safety, identification publicity, operational expertise safety, connect floor administration, and threat evaluation. | Sure | Sure |
| ESET | $275 for 5 gadgets per 12 months for the ESET Defend bundle that features ESET Vulnerability and Patch Administration | Cloud-based. A separate on-prem suite is obtainable that features vulnerability administration | EDR, server safety, cell risk protection, encryption, risk protection, cloud safety, vulnerability & patch administration, MFA, and MDR | Some automated discovery however not as broad as a few of the others | Some auto-remediation capabilities are included |
| Syxsense | $9 per gadget per thirty days or $960 per 12 months for 10 gadgets | One model for the cloud and one other for on prem | Patch administration, vulnerability scanning, IT administration, cell gadget administration, and 0 belief | Sure | Sure |
| CrowdStrike | $184 per 12 months for the complete suite and about $40 per 12 months for Publicity Administration | Cloud-based | EDR, antivirus, risk looking/intelligence, publicity administration, AI, risk looking, cloud safety, SIEM, information safety, automation | Sure | Sure |
| Qualys | $295 per 12 months for the small enterprise model and about $2000 for the enterprise model. | Cloud-based with an on-prem model accessible. | Asset administration, vulnerability & configuration administration, threat remediation, risk detection & response, EDR, cloud safety, and compliance. | Sure | Sure |
| Rapid7 | $6 per thirty days per asset or $2 per thirty days per asset for a 500-asset license. | Cloud and on-prem | AI engine, XDR, publicity administration, and assault floor administration. | Sure | Sure |
| Ivanti | $4 per thirty days per person. | Cloud or on-prem | Discovery, IT automation, real-time perception, endpoint administration, community and endpoint safety, provide chain, and repair and asset administration. | Sure | Sure |
| StorageGuard | $200 per thirty days for as much as 50 programs. | Cloud | No | Sure | Restricted |
Tenable Vulnerability Administration: Greatest total

Tenable Vulnerability Administration takes a risk-based method to vulnerability administration. It focuses on community visibility as a way to predict when assaults will happen and to have the ability to reply quickly when vital vulnerabilities are in play. A 60-day free trial is obtainable.
SEE: Easy methods to Create an Efficient Cybersecurity Consciousness Program (TechRepublic Premium)
Why I selected Tenable
I chosen Tenable as the most effective total vulnerability administration software total for a lot of causes. It’s the market chief amongst vulnerability administration instruments with a 25% market share. It features a wealth of options and ticks nearly all of the packing containers. It accommodates lots of of integrations with different platforms and safety instruments that make automation of workflows straightforward and cut back the variety of sources wanted to maintain the enterprise protected.
Pricing
- Tenable prices about $4,000 per 12 months for 100 belongings.
Options
- The Tenable Group is lively with loads of customers keen to help you to deal with issues.
- Energetic and passive scanning of on-premise programs, digital machines, cloud situations, and cell gadgets.
- Cloud Connectors give steady visibility and evaluation into public cloud environments like Microsoft Azure, Google Cloud Platform, and Amazon Internet Providers.
- Constructed-in prioritization, risk intelligence, and real-time reporting assist customers to know threat and proactively disrupt assault paths.
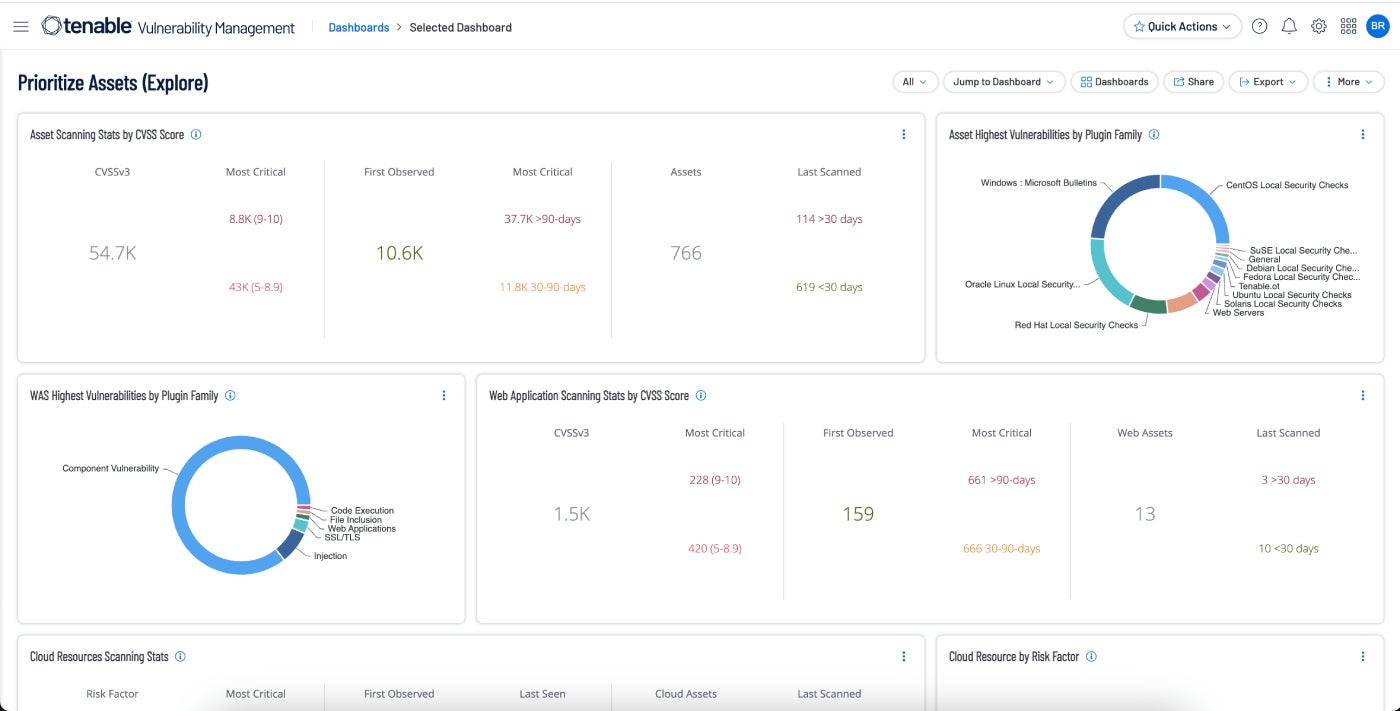
Execs and cons
| Execs | Cons |
|---|---|
| Totally built-in into the broader Tenable One platform. | Some customers report that assist may very well be improved. |
| Steady, always-on discovery and evaluation | Actual-time scanning and total scanning velocity may very well be improved. |
| Risk intelligence | Not the most affordable resolution in the marketplace. |
| Automated vulnerability prioritization. | Higher suited to skilled IT professionals |
| Actual-time visualization of threat, and monitoring of vulnerabilities, belongings, and remediations. | |
| Vulnerability threat scores to determine threat. |
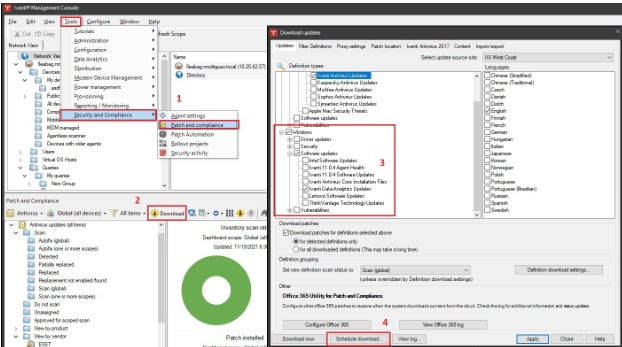
ESET Vulnerability and Patch Administration: Greatest for SMEs

ESET Vulnerability and Patch Administration can robotically scan hundreds of functions for any of tens of hundreds of frequent vulnerabilities and exposures. It will probably prioritize and filter vulnerabilities by publicity rating and severity.
Why I selected ESET Vulnerability and Patch Administration
I favored ESET as it’s straightforward to put in and run. This makes it enticing for SMEs and bigger organizations that lack IT and cybersecurity sources.
Pricing
- $275 for 5 gadgets per 12 months for the ESET Defend bundle that features ESET Vulnerability and Patch Administration.
Options
- Helps a number of variations of Home windows, Linux, and macOS.
- Detects over 35,000 CVEs.
- Automated scans with customizable schedule settings.
- Prioritizes and filters vulnerabilities by publicity rating and severity.
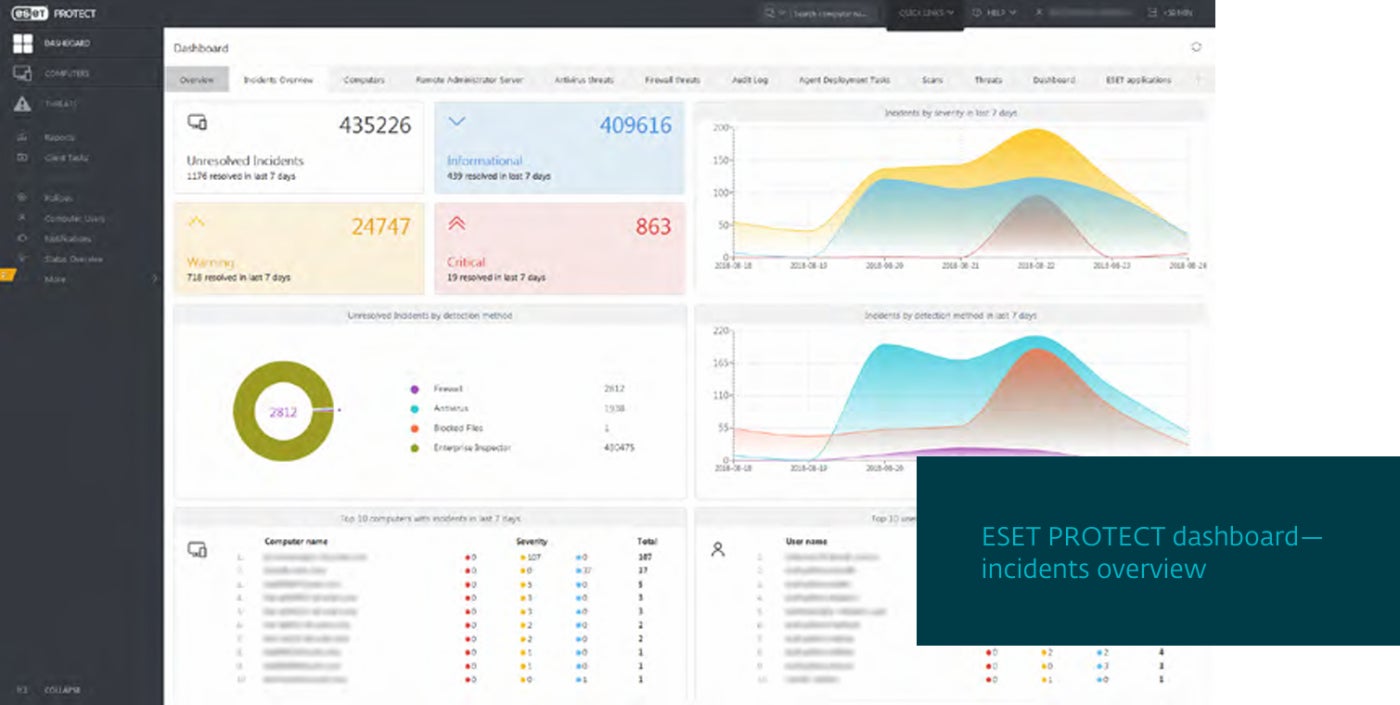
Execs and cons
| Execs | Cons |
|---|---|
| Simplifies patching by prioritizing vital belongings and scheduling the rest for off-peak occasions. | Automated discovery and remediation options lack the scope of another options. |
| Safety in opposition to ransomware and zero-day threats. | Extra centered on small and mid-size organizations slightly than the enterprise market. |
| Straightforward to arrange, use, and keep. |
Syxsense Enterprise: Greatest for patch administration

Syxsense Enterprise consists of patch administration, vulnerability scanning, IT administration, and cell gadget administration inside its vulnerability administration platform. Most lately, it has added built-in remediation options in addition to zero belief. Every part is now mixed into one console by way of Syxsense Enterprise.
Why I selected Syxsense
Syxsense started life as a patch administration specialist. Constructing on that success, it has steadily expanded right into a full featured vulnerability administration suite. Nevertheless, I observed that it doesn’t embody the breadth of safety modules that lots of the different distributors on this information. It’s lacking SIEM, risk intelligence, and antivirus, for instance. Regardless of that, I favored the tight concentrate on vulnerability and gadget administration. For people who have already got a safety platform and simply wish to enhance patch administration and vulnerability administration, Syxsense is an efficient alternative.
Pricing
- $9 per gadget per thirty days or $960 per 12 months for 10 gadgets.
Options
- Automated discovery and remediation workflows.
- Complete patch administration together with patch supersedence, patch rollback, and patching any endpoint together with cell gadgets.
- A Zero Belief Analysis Engine creates a trusted safety posture for endpoints.
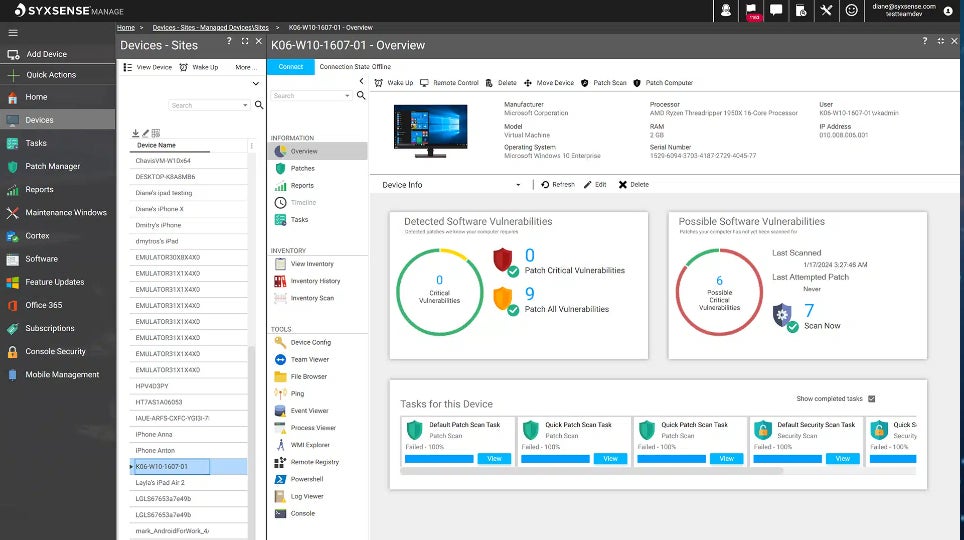
Execs and cons
| Execs | Cons |
|---|---|
| Wonderful patch administration performance. | Syxsense was simply acquired by Absolute Safety, which might impede the excessive degree of steady innovation that propelled Syxsense to the forefront of the patch and vulnerability administration area. |
| Tightly centered on vulnerability administration. | Suite is lacking components akin to antivirus, risk looking, and SIEM. |
| Separate variations for cloud and on-prem. |
CrowdStrike Publicity Administration: Greatest cybersecurity suite incorporating vulnerability administration

CrowdStrike Publicity Administration grew out of an older product generally known as Falcon Highlight, which I used to be already acquainted with. I observed the way it broadens the capabilities of Falcon Highlight by including extra of a threat administration method together with a number of AI-based capabilities.
Why I selected CrowdStrike Publicity Administration
CrowdStrike Publicity Administration is a strong product in its personal proper. It’s one a part of a complete suite with a variety of security measures. Most consumers will buy the whole CrowdStrike platform slightly than solely the Publicity Administration ingredient. Generally known as the CrowdStrike Falcon Platform, it encompasses EDR, antivirus, risk looking/intelligence, publicity administration, AI, risk looking, cloud safety, SIEM, information safety, automation, and extra, all from a single agent. Anybody needing a vulnerability administration software and a brand new safety suite can’t go far mistaken adopting your complete Falcon Platform.
Pricing
- $184 per 12 months for the complete suite and about $40 per 12 months for the publicity administration module.
Options
- Automated evaluation for vulnerabilities, whether or not on or off the community.
- Shortened time-to-respond with real-time visibility into vulnerabilities and threats.
- The power to prioritize and predict which vulnerabilities are most certainly to have an effect on the group.
- The corporate boasts a single lightweight-agent structure.
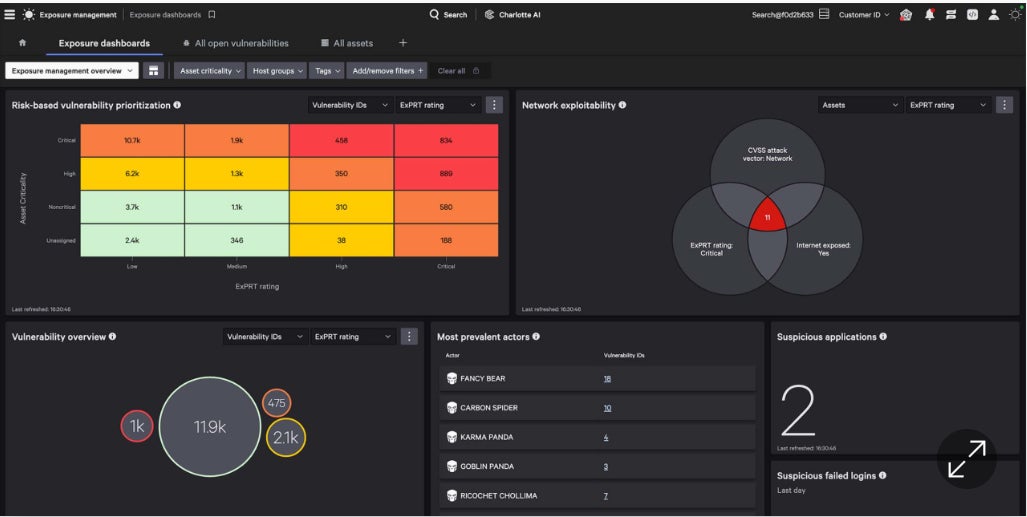
Execs and cons
| Execs | Cons |
|---|---|
| Vulnerability and patching orchestration. | Restricted capabilities relating to scanning for misconfigurations in safety functions. |
| Integration inside the CrowdStrike Falcon. | Extra concentrate on your complete suite than on vulnerability administration. |
| AI ties collectively risk intelligence with vulnerability evaluation in actual time. | |
| A single agent for all modules. |
Qualys VMDR: Greatest for cloud-based enterprises

Qualys Vulnerability Administration Detection and Response takes the context of threats under consideration as a strategy to prioritize and remediate critical threats quickly. I appreciated the worth of its automated scoring methodology, generally known as TruRisk.
Why I selected Qualys VMDR
Qualys VMDR does a superb job bringing collectively a set of key safety features, together with vulnerability evaluation, asset discovery, stock administration, and assault floor administration. It’s half of a big, cloud-based suite of safety merchandise. As such, I take into account it to be a sensible choice for enterprises and bigger companies working within the cloud.
Pricing
- Qualys pricing appeared fairly complicated to me. It’s based mostly on the quantity or compute models within the cloud: digital machines, serverless, and container pictures. The unit worth varies based mostly on variations within the performance, complexity, and total worth proposition of every module. The enterprise model of your complete suite begins at about $500 per thirty days and ramps up from there based mostly on the variety of customers. The vulnerability administration module is alleged to be accessible to small companies beginning at $250 per 12 months and $2000 for enterprises.
Options
- Primarily cloud-based however an on-prem personal cloud equipment is obtainable for purchasers with strict information sovereignty necessities.
- A cloud-based service supplied primarily to SMEs supplies VMDR together with endpoint detection and response and patch administration instruments.
- Threat-based and context-based prioritization of threats
- Integration with patch administration, stock administration, and ITSM.
- Qualys Risk Analysis Unit proactively searches for brand new threats by analyzing information from its person base, dozens of risk intelligence feeds, third-party information, and the darkish internet.
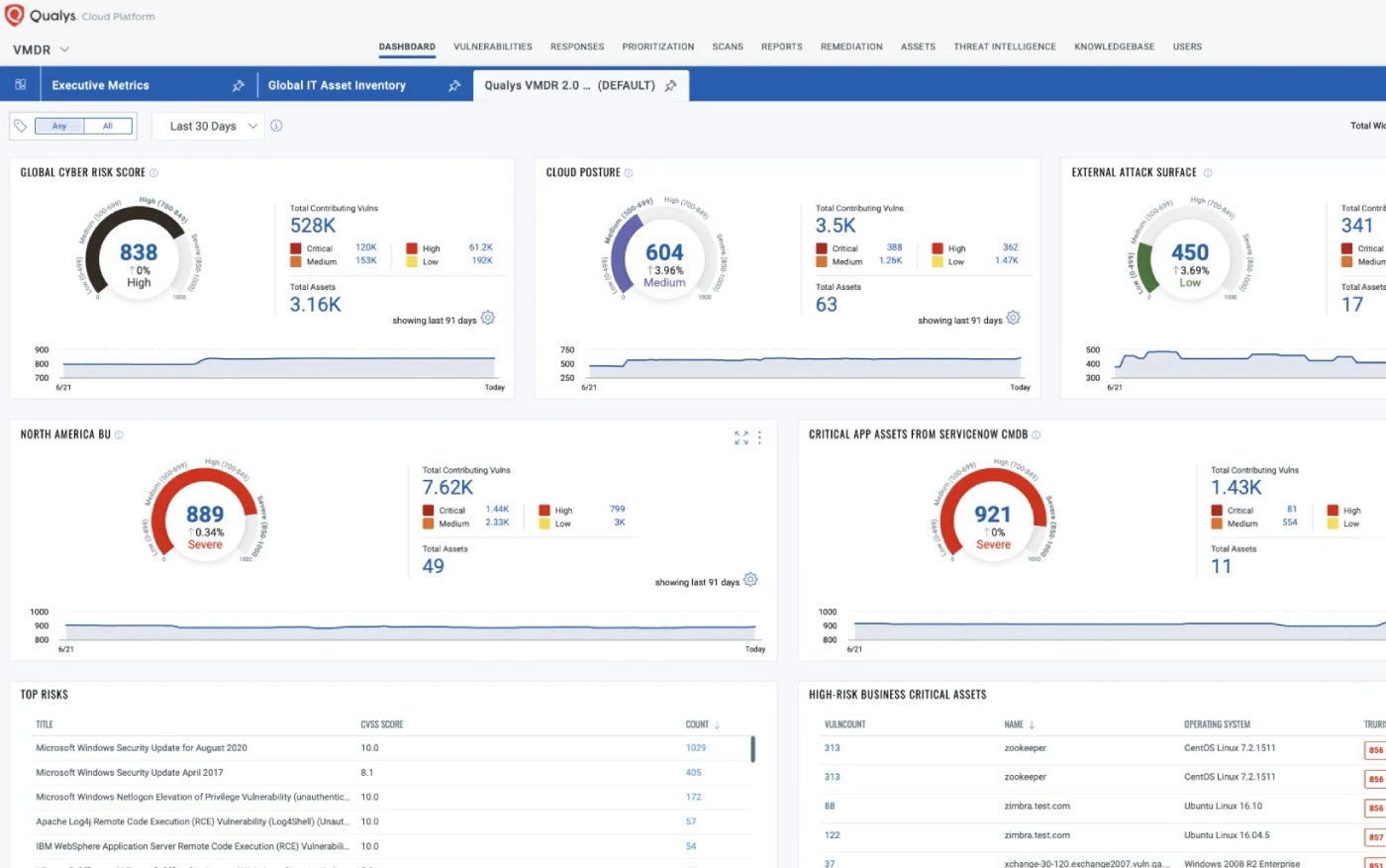
Execs and cons
| Execs | Cons |
|---|---|
| Broad vary of vulnerability signature databases. | May be difficult to put in, study, and use for much less mature IT outlets. |
| Actual-time detection of vulnerabilities akin to patches that should be put in and misconfigurations. | Cloud and hypervisor assist may very well be improved. |
| Robotically detects the most recent superseding patch for the susceptible asset and deploys it. | |
| Qualys is without doubt one of the market leaders in vulnerability administration based mostly on market share. |
Options
- Frequently assesses and prioritizes vital vulnerabilities utilizing threat scoring from 1 to 1000.
- Tracks compliance in opposition to coverage and rules, and compares to trade benchmarks.
- Rapid7 Labs helps determine all internet-facing belongings and alert on vulnerabilities.
- Good scanning consistency and vary of gadgets.
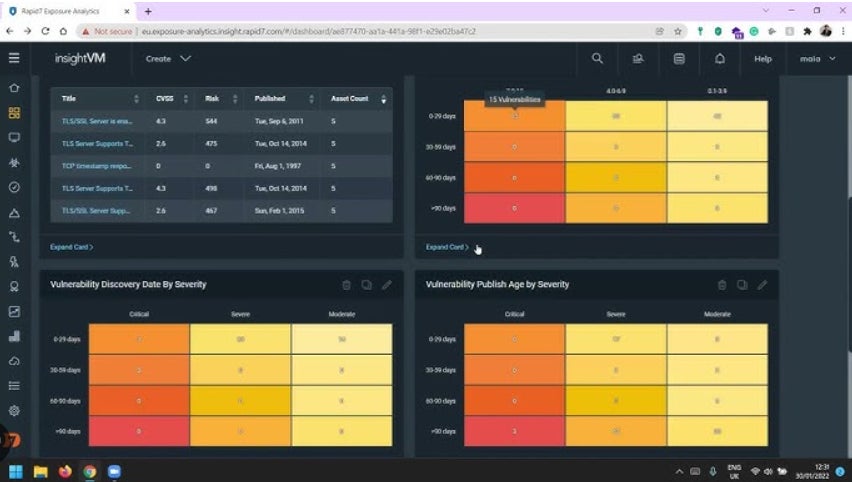
Execs and cons
| Execs | Cons |
|---|---|
| Automated remediation. | Greatest suited to educated safety groups. |
| Automated pen-testing. | Can typically be sophisticated to arrange. |
| One of many high vulnerability administration distributors per market share. | Some customers word integration and deployment points |
| Runs vulnerability scans throughout cloud, bodily, and digital infrastructure and robotically collects information from all endpoints. | Assist responsiveness may very well be improved. |
| Safety groups can streamline remediation actions akin to vulnerability patching and containment. | |
| Integrates with a variety of third-party instruments together with ticketing programs, patch administration options, and SIEM. |
Ivanti VMaaS: Greatest as a service providing

Ivanti has a protracted historical past as a high vulnerability administration vendor. It affords instruments you’ll be able to deploy inside the enterprise or as a service.
Why I selected Ivanti VMaaS
For me, Ivanti VMaaS stands out resulting from its pairing of vulnerability administration as-a-service with skilled safety analysts, scanning instruments, and processes that assist companies determine vulnerabilities on the community and in functions. However the firm additionally affords high cloud-based instruments akin to Ivanti Neurons for risk-based vulnerability administration.
Pricing
Options
- Ivanti Neurons for RBVM, can ingest information from a number of third-party scanners to assist shut gaps and blind spots.
- It robotically analyzes information from vulnerability scanners and supplies perception to IT and safety groups.
- Scan findings are robotically correlated and contextualized with risk information and evaluation, and prioritized.
- Finds code weak point and pinpoints coding errors.
Execs and cons
| Execs | Cons |
|---|---|
| This absolutely managed service frees up personnel for different initiatives. | Some customers complain of lack of assist. |
| Straightforward-to-follow remediation plans. | Customization choices are restricted. |
| Threat scoring ensures remediation suggestions are centered on actions that concentrate on probably the most critical threats. | Aggressive patch administration merchandise could also be extra complete at discovering all endpoints working on the community. |
| Automated workflows. |
StorageGuard: Greatest for storage and backup functions

StorageGuard by Continuity Software program scans, detects, and fixes safety misconfigurations and vulnerabilities throughout lots of of storage, backup, and information safety programs.
Why I selected StorageGuard
Most instruments on this information present broad protection — both throughout your complete vulnerability administration panorama or are a part of giant safety suites that go far past vulnerability administration. I picked StorageGuard because it takes the alternative method. It’s laser-focused on one side of this market: a complete handle to a significant hole discovered in lots of vulnerability administration merchandise — storage and backup vulnerabilities and misconfigurations. StorageGuard fills that area of interest so effectively that I like to recommend its use along with a few of the different instruments listed right here.
Pricing
- $200 per thirty days for as much as 50 programs.
Options
- Straight addresses the vulnerabilities and potential threats listed by NIST in Safety Pointers for Storage Infrastructure.
- Broad protection of storage and backup apps and programs from the likes of Dell, NetApp, Hitachi Vantara, Pure, Rubrik, Commvault, Veritas, HPE, Brocade, Cisco, Veeam, Cohesity, IBM, Infinidat, VMware, AWS, and Azure.
- Can detect deviation from a selected configuration baseline.
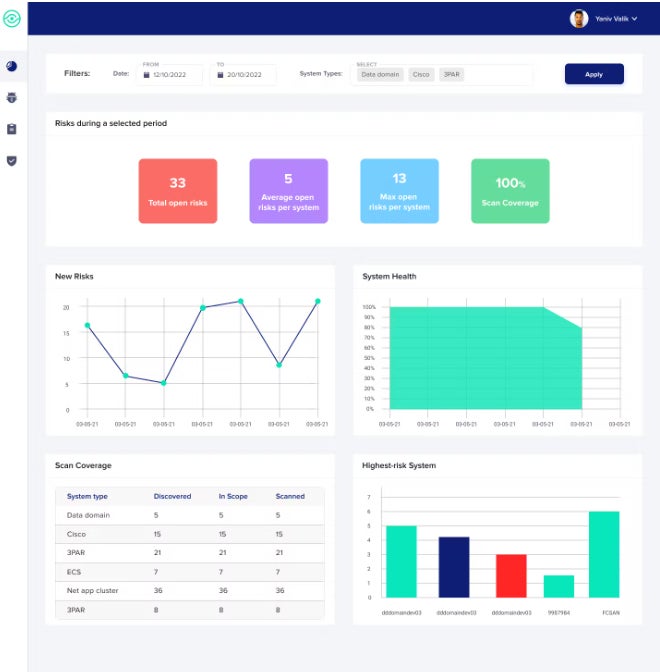
Execs and cons
| Execs | Cons |
|---|---|
| Scans and finds weaknesses in storage and backup functions that different scanners miss. | Doesn’t handle conventional vulnerabilities in third celebration functions and OSes. |
| Customers touch upon ease of use and thoroughness to find backup and storage misconfigurations. | Centered primarily on discovery of points versus decision. |
| Supplies proof of audit compliance in opposition to CIS Controls, NIST, ISO, PCI, NERC CIP, and others. |
Vulnerability administration: Continuously requested questions
What are vulnerability administration instruments?
In accordance with NIST, vulnerability administration is a “functionality that identifies vulnerabilities [common vulnerabilities and exposures] on gadgets which can be possible for use by attackers to compromise a tool and use it as a platform from which to increase compromise to the community.”
In addition to mitigating configuration or code points which may enable an attacker to take advantage of an surroundings, the definition is usually broadened to incorporate patch administration, MDM, IT asset administration, and EDR. The vulnerability administration operate is usually built-in into a big safety suite.
How do vulnerability administration instruments work?
Vulnerability administration will be damaged right into a collection of steps, lots of which are actually automated:
- Vulnerability scanning.
- Reporting on any vulnerabilities found and prioritization based mostly on their potential affect on the enterprise.
- Deployment of remediation or advice of remediation steps.
- Validation of remediations to make sure points have been resolved.
- Reporting on the state of vulnerabilities and their decision inside the enterprise.
How are vulnerability administration instruments deployed?
They are often deployed as on-premises software program, delivered as SaaS, or as managed companies.
What’s vulnerability administration as a service?
Vulnerability administration as a managed service is delivered by a supplier by way of the cloud slightly than downloading and working on-prem software program. It constantly identifies, assesses, experiences, and manages vulnerabilities throughout cloud identities, workloads, platform configurations, and infrastructure.
What options ought to I search for in a high vulnerability administration software?
Sure core features are current in all high vulnerability administration platforms. These embrace:
- Discovery of all gadgets, functions, and programs and detection of potential vulnerabilities and misconfigurations that will exist anyplace inside the community on any gadget that connects to the community.
- A database of vulnerabilities and threats that’s constantly up to date.
- Integration with a variety of platforms, safety programs, vulnerability scanners, ticketing programs, and different safety instruments.
- A technique of threat scoring and prioritization.
- Automated remediation or remediation steering.
- Reporting capabilities that spotlight points and compliance.
How do I select the most effective vulnerability administration software for my enterprise?
These searching for a vulnerability administration software ought to ask questions akin to:
- What platforms does the software function on? Bear in mind that some are centered on Linux, some on Home windows, and a few cowl a number of or all OS and platforms. Additionally bear in mind what workers are already educated on. Don’t add Linux instruments in case your inside personnel are educated on Home windows, and vice-versa.
- What endpoints are coated? Some deal primarily with servers, PCs, and laptops, whereas others prolong to smartphones, IoT, wi-fi, and different gadgets.
- Which components of the safety panorama are you trying so as to add or improve past vulnerability administration? In case you are within the midst of a whole overhaul of your complete safety infrastructure, begin with the suite after which discover one that features the vulnerability administration options you want. But when you have already got a strong safety spine, concentrate on vulnerability administration instruments that present the protection you want.
- Take note of the positive print in contrasts and look carefully at price construction, the potential for added charges, assist prices, and so on.
- Don’t be caught on one vendor for all safety wants. Vendor A may go for many of your safety infrastructure, however Vendor B could also be higher at vulnerability administration.
- What do analysts akin to Gartner say in regards to the totally different instruments, their market share, their execs and cons, and future course?
No matter software you select from the listing above, the advantages of vulnerability administration shortly present up by way of fewer breaches, information that’s higher safeguarded, assaults being noticed far sooner than earlier than, and added automation.
Methodology
The instruments coated right here had been chosen based mostly on analyst experiences, peer evaluations, and person satisfaction, in addition to evaluations posted in TechRepublic and different Know-how Recommendation websites. I additionally supplied a mixture of full-fledged vulnerability administration merchandise, extremely specialised instruments, and people the place vulnerability administration is one module inside a a lot bigger suite.


