The Chinese language firm in control of handing out domains ending in “.high” has been given till mid-August 2024 to point out that it has put in place techniques for managing phishing reviews and suspending abusive domains, or else forfeit its license to promote domains. The warning comes amid the discharge of latest findings that .high was the commonest suffix in phishing web sites over the previous 12 months, second solely to domains ending in “.com.”

Picture: Shutterstock.
On July 16, the Web Company for Assigned Names and Numbers (ICANN) despatched a letter to the house owners of the .high area registry. ICANN has filed lots of of enforcement actions towards area registrars over time, however on this case ICANN singled out a site registry liable for sustaining a complete top-level area (TLD).
Amongst different causes, the missive chided the registry for failing to answer reviews about phishing assaults involving .high domains.
“Primarily based on the data and information gathered via a number of weeks, it was decided that .TOP Registry doesn’t have a course of in place to promptly, comprehensively, and fairly examine and act on reviews of DNS Abuse,” the ICANN letter reads (PDF).
ICANN’s warning redacted the identify of the recipient, however information present the .high registry is operated by a Chinese language entity known as Jiangsu Bangning Science & Know-how Co. Ltd. Representatives for the corporate haven’t responded to requests for remark.
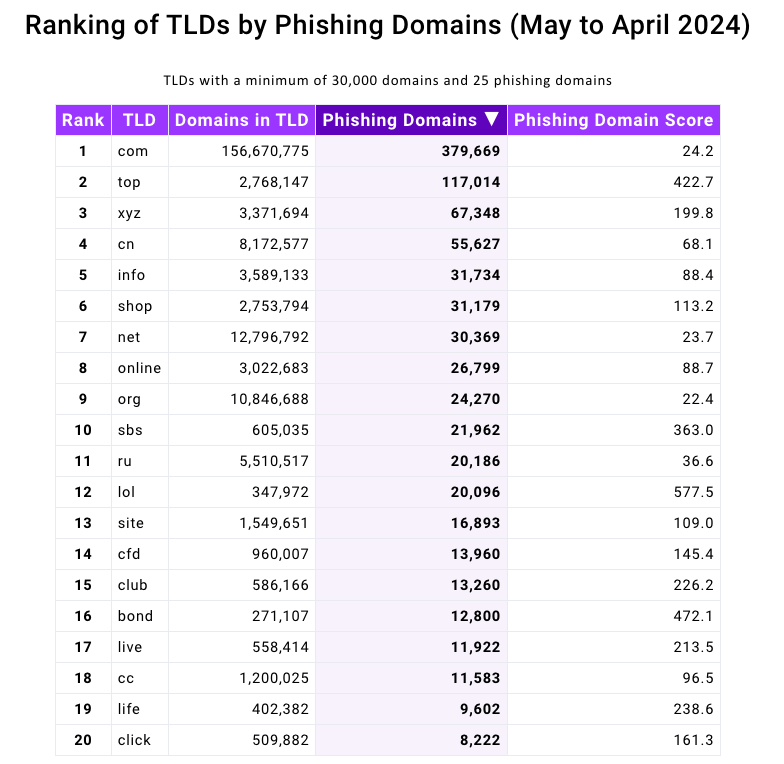
Domains ending in .high have been represented prominently in a brand new phishing report launched at this time by the Interisle Consulting Group, which sources phishing knowledge from a number of locations, together with the Anti-Phishing Working Group (APWG), OpenPhish, PhishTank, and Spamhaus.
Interisle’s latest examine examined almost two million phishing assaults within the final 12 months, and located that phishing websites accounted for greater than 4 p.c of all new .high domains between Might 2023 and April 2024. Interisle stated .high has roughly 2.76 million domains in its steady, and that greater than 117,000 of these have been phishing websites prior to now 12 months.
Supply: Interisle Consulting Group.
ICANN stated its evaluate was primarily based on data collected and studied about .high domains over the previous few weeks. However the truth that excessive volumes of phishing websites are being registered via Jiangsu Bangning Science & Know-how Co Ltd. is hardly a brand new development.
For instance, greater than 10 years in the past the identical Chinese language registrar was the fourth commonest supply of phishing web sites, as tracked by the APWG. Keep in mind that the APWG report excerpted under was printed greater than a 12 months earlier than Jiangsu Bangning obtained ICANN approval to introduce and administer the brand new .high registry.
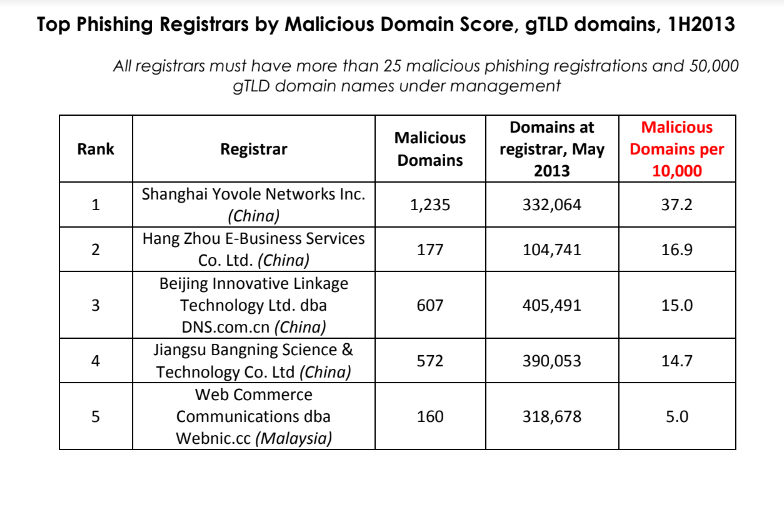
Supply: APWG phishing report from 2013, two years earlier than .high got here into being.
A captivating new wrinkle within the phishing panorama is the expansion in rip-off pages hosted through the InterPlanetary File System (IPFS), a decentralized knowledge storage and supply community that’s primarily based on peer-to-peer networking. In keeping with Interisle, using IPFS to host and launch phishing assaults — which may make phishing websites tougher to take down — elevated a staggering 1,300 p.c, to roughly 19,000 phishing websites reported within the final 12 months.
Final 12 months’s report from Interisle discovered that domains ending in “.us” — the top-level area for america — have been among the many most prevalent in phishing scams. Whereas .us domains should not even on the High 20 record of this 12 months’s examine, “.com” maintained its perennial #1 spot as the most important supply of phishing domains general.
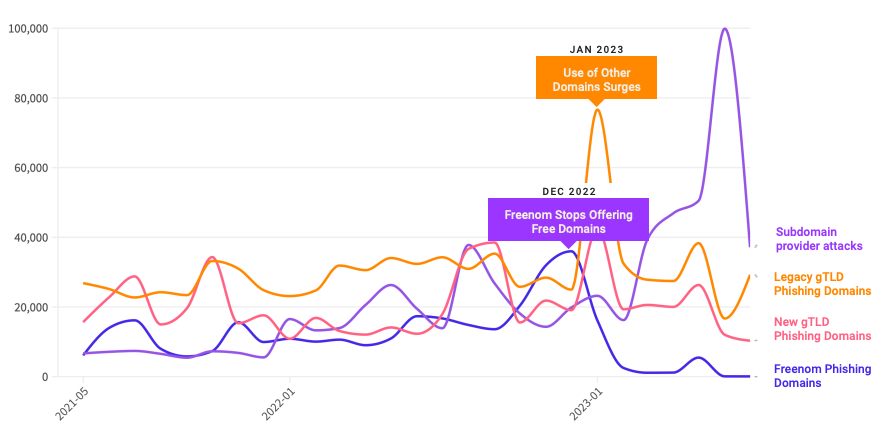
A 12 months in the past, the phishiest area registrar by far was Freenom, a now-defunct registrar that handed out free domains in a number of country-code TLDs, together with .tk, .ml, .ga and .cf. Freenom went out of enterprise after being sued by Meta, which alleged Freenom ignored abuse complaints whereas monetizing site visitors to abusive domains.
Following Freenom’s demise, phishers shortly migrated to different new low-cost TLDs and to providers that enable nameless, free area registrations — notably subdomain providers. For instance, Interisle discovered phishing assaults involving web sites created on Google’s blogspot.com skyrocketed final 12 months greater than 230 p.c. Different subdomain providers that noticed a considerable progress in domains registered by phishers embody weebly.com, github.io, wix.com, and ChangeIP, the report notes.
Interisle Consulting associate Dave Piscitello stated ICANN may simply ship related warning letters to no less than a half-dozen different top-level area registries, noting that spammers and phishers are inclined to cycle via the identical TLDs periodically — together with .xyz, .data, .assist and .lol, all of which noticed significantly extra enterprise from phishers after Freenom’s implosion.
Piscitello stated area registrars and registries may considerably scale back the variety of phishing websites registered via their providers simply by flagging clients who attempt to register big volumes of domains without delay. Their examine discovered that no less than 27% of the domains used for phishing have been registered in bulk — i.e. the identical registrant paid for lots of or 1000’s of domains in fast succession.
The report features a case examine during which a phisher this 12 months registered 17,562 domains over the course of an eight-hour interval — roughly 38 domains per minute — utilizing .lol domains that have been all composed of random letters.
ICANN tries to resolve contract disputes privately with the registry and registrar group, and consultants say the nonprofit group often solely publishes enforcement letters when the recipient is ignoring its personal notices. Certainly, ICANN’s letter notes Jiangsu Bangning didn’t even open its emailed notifications. It additionally cited the registry for falling behind in its ICANN membership charges.
With that in thoughts, a evaluate of ICANN’s public enforcement exercise suggests two developments: One is that there have been far fewer public compliance and enforcement actions lately — even because the variety of new TLDs has expanded dramatically.
The second is that in a majority of circumstances, the failure of a registry or registrar to pay its annual ICANN membership charges was cited as a motive for a warning letter. A evaluate of almost two dozen enforcement letters ICANN has despatched to area registrars since 2022 reveals that failure to pay dues was cited as a motive (or the motive) for the violation no less than 75 p.c of the time.
Piscitello, a former vp of safety at ICANN, stated almost all breach notices despatched out whereas he was at ICANN have been as a result of the registrar owed cash.
“I feel the remainder is simply lipstick to recommend that ICANN’s on high of DNS Abuse,” Piscitello stated.
KrebsOnSecurity has sought remark from ICANN and can replace this story in the event that they reply.
ICANN stated most of its investigations are resolved and closed via the preliminary casual decision stage, and that lots of of enforcement circumstances are initiated throughout this stage with the contracted events who’re required to exhibit compliance, turn into compliant, and/or current and implement remediation plans to forestall the recurrence of these enforcement points.
“It is very important consider that, previous to issuing any discover of breach to a registrar or registry operator, ICANN Compliance conducts an general contractual compliance ‘well being verify’ of the related contracted celebration,” ICANN stated in a written response to questions. “Throughout this verify, ICANN Compliance proactively evaluations the contracted celebration’s compliance with obligations throughout the agreements and insurance policies. Any extra contractual violation discovered throughout these checks is added to the Discover of Breach. It’s not unusual for events who didn’t adjust to contractual obligations (whether or not they’re associated to DNS Abuse, RDDS, or others) to even be in arrears with ICANN charges.”
Replace, 11:49 p.m. ET: Added assertion from ICANN. Clarified Piscitello’s former function at ICANN.