The top of safety advocacy at Datadog, a cloud-based monitoring and analytics platform, has urged enterprises in Australia and the APAC area to speed up phasing out long-lived credentials for fashionable hyperscale cloud companies, warning that they continue to be a severe information breach danger.
Talking with TechRepublic, Andrew Krug highlighted findings from Datadog’s State of Cloud Safety 2024 report, which recognized long-lived credentials as a persistent safety danger issue. Whereas credential administration practices are bettering, Krug famous they don’t seem to be advancing as rapidly or successfully as wanted to mitigate dangers.
Lengthy-lived credentials are nonetheless an enormous risk to cloud safety
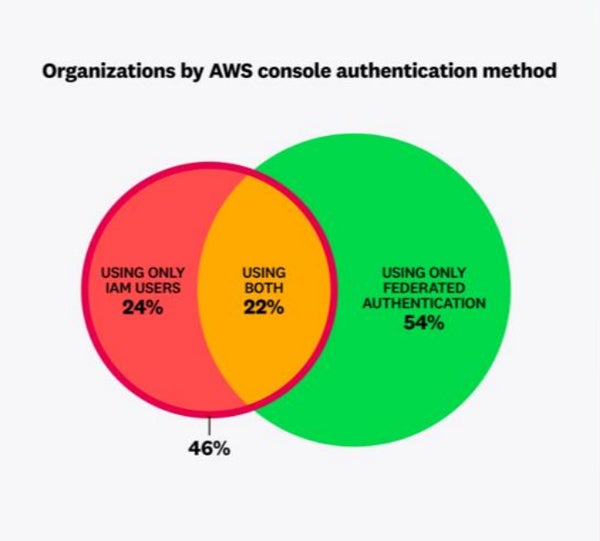
The report revealed that almost half (46%) of organisations utilizing AWS depend on IAM customers for human entry to cloud environments — a observe Datadog known as a type of long-lived credential. This was true even for organisations utilizing centralised identification administration to grant entry throughout a number of techniques.
Furthermore, almost one in 4 relied solely on IAM customers with out implementing centralised federated authentication. In line with Datadog, this highlights a persistent problem: whereas centralised identification administration is turning into extra frequent, unmanaged customers with long-lived credentials proceed to pose a major safety danger.
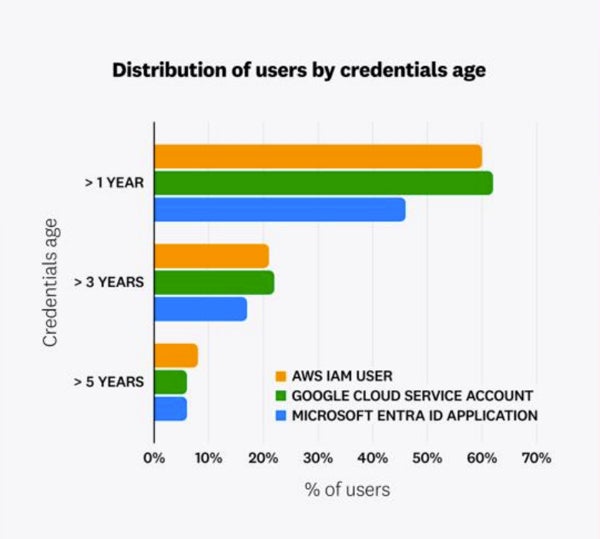
The prevalence of long-lived credentials spans all main cloud suppliers and sometimes consists of outdated or unused entry keys. The report discovered that 62% of Google Cloud service accounts, 60% of AWS IAM customers, and 46% of Microsoft Entra ID purposes had entry keys that had been greater than a 12 months outdated.
Lengthy-lived credentials include a major danger of information breaches
Lengthy-lived cloud credentials by no means expire and continuously get leaked in supply code, container pictures, construct logs, and utility artifacts, in accordance with Datadog. Previous analysis carried out by the corporate has proven they’re the most typical reason for publicly documented cloud safety breaches.
SEE: The highest 5 cybersecurity traits for 2025
Krug mentioned there’s mature tooling out there to make sure secrets and techniques don’t find yourself in manufacturing environments, comparable to static code evaluation. Datadog’s report additionally notes the rise of IMDSv2 enforcement in AWS EC2 cases, an essential safety mechanism to dam credential theft.
There are much less long-lived credentials, however change is simply too sluggish
There have been strikes to mitigate the issue, comparable to AWS launching IAM Id Centre, permitting organisations to centrally handle entry to AWS purposes. Whereas corporations are within the course of of adjusting to the service, Krug mentioned, “I simply don’t know that everybody considers this their highest precedence.”
“It positively must be, as a result of if we look on the final 10 years of information breaches, the first theme is that long-lived entry key pairs had been the basis reason for these information breaches mixed with overly permissive entry,” he defined. “If we eradicate one aspect of that, we actually considerably cut back the chance for the enterprise.”
The long-lived credentials downside isn’t unique to APAC — it’s a world problem
In line with Krug, APAC is not any totally different from the remainder of the world. With no regulation to manage the administration of long-lived credentials within the cloud in any explicit jurisdiction, corporations worldwide use comparable approaches with comparable cloud suppliers, usually throughout a number of world jurisdictions.
What’s stopping the transfer away from long-lived credentials?
The hassle required to transition groups to single sign-on and momentary credentials has slowed the adoption of those practices. Krug mentioned the “elevate and shift” concerned in migrating improvement workflows to single sign-on may be appreciable. That is partly because of the mindset shift required and partly as a result of organisations should present satisfactory help and steering to assist groups adapt.
Nevertheless, he famous that instruments like AWS Id Centre, which has been out there for 3 years, have made this transition extra possible. These instruments are designed to scale back developer friction by streamlining the authentication course of, minimising the necessity for repeated MFA sign-ins repeatedly, and making certain that workflows stay environment friendly.
SEE: How AI is amplifying the dangers of information within the cloud
“AWS Id Centre is a good product and allows these very seamless person flows, however people are nonetheless midstream in migrating to it,” Krug mentioned.
What must you do together with your long-lived credentials?
Datadog’s report warned that it’s unrealistic to anticipate that long-lived credentials may be securely managed. The seller recommends that corporations undertake safe identities with fashionable authentication mechanisms, leverage short-lived credentials, and actively monitor adjustments to APIs that attackers generally use.
“Organisations ought to leverage mechanisms that present time-bound, momentary credentials,” the report mentioned.
Workloads. For workloads, Datadog mentioned this finish may be achieved with IAM roles for EC2 cases or EKS Pod Id in AWS, Managed Identities in Microsoft Azure, and repair accounts connected to workloads for Google Cloud if the organisation makes use of the foremost world hyperscalers.
People: For human customers, Datadog mentioned the best resolution is to centralise identification administration utilizing an answer like AWS IAM Id Heart, Okta, or Microsoft Entra ID and keep away from utilizing particular person cloud customers for every worker, which it labelled “extremely inefficient and dangerous.”


