By the point modifications have made their strategy to the legacy database, then you could possibly argue that it’s too late for
occasion interception.
That stated, “Pre-commit” triggers can be utilized to intercept a database write occasion and take completely different actions.
For instance a row may very well be inserted right into a separate Occasions desk to be learn/processed by a brand new part –
while continuing with the write as earlier than (or aborting it).
Be aware that important care needs to be taken in the event you change the prevailing write behaviour as you could be breaking
an important implicit contract.
Case Research: Incremental area extraction
One in all our groups was working for a shopper whose legacy system had stability points and had grow to be troublesome to keep up and sluggish to replace.
The organisation was trying to treatment this, and it had been determined that probably the most acceptable method ahead for them was to displace the legacy system with capabilities realised by a Service Based mostly Structure.
The technique that the workforce adopted was to make use of the Strangler Fig sample and extract domains, one by one, till there was little to not one of the authentic software left.
Different concerns that have been in play included:
- The necessity to proceed to make use of the legacy system with out interruption
- The necessity to proceed to permit upkeep and enhancement to the legacy system (although minimising modifications to domains being extracted was allowed)
- Adjustments to the legacy software have been to be minimised – there was an acute scarcity of retained information of the legacy system
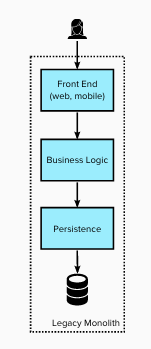
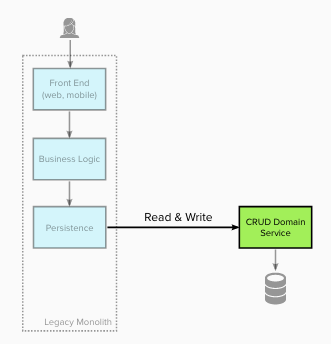
Legacy state
The diagram under reveals the structure of the legacy
structure. The monolithic system’s
structure was primarily Presentation-Area-Information Layers.
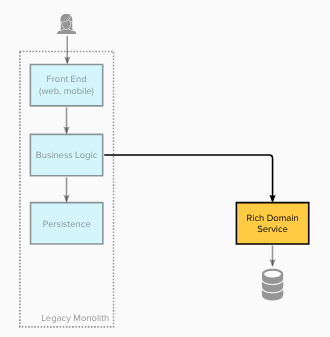
Stage 1 – Darkish launch service(s) for a single area
Firstly the workforce created a set of providers for a single enterprise area together with the aptitude for the information
uncovered by these providers to remain in sync with the legacy system.
The providers used Darkish Launching – i.e. not utilized by any customers, as an alternative the providers allowed the workforce to
validate that knowledge migration and synchronisation achieved 100% parity with the legacy datastore.
The place there have been points with reconciliation checks, the workforce may motive about, and repair them guaranteeing
consistency was achieved – with out enterprise affect.
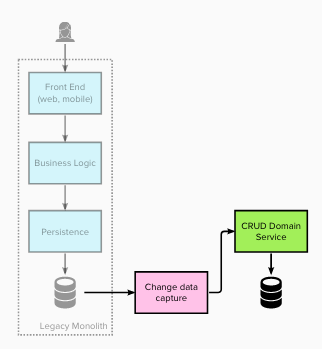
The migration of historic knowledge was achieved by way of a “single shot” knowledge migration course of. While not strictly Occasion Interception, the continued
synchronisation was achieved utilizing a Change Information Seize (CDC) course of.
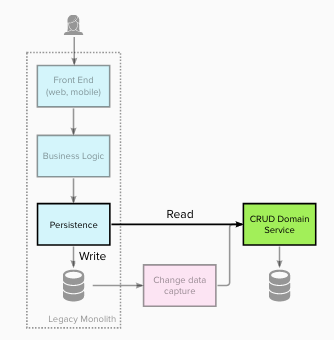
Stage 2 – Intercept all reads and redirect to the brand new service(s)
For stage 2 the workforce up to date the legacy Persistence Layer to intercept and redirect all of the learn operations (for this area) to
retrieve the information from the brand new area service(s). Write operations nonetheless utilised the legacy knowledge retailer. That is
and instance of Department by Abstraction – the interface of the Persistence Layer stays unchanged and a brand new underlying implementation
put in place.
Stage 3 – Intercept all writes and redirect to the brand new service(s)
At stage 3 numerous modifications occurred. Write operations (for the area) have been intercepted and redirected to create/replace/take away
knowledge inside the new area service(s).
This transformation made the brand new area service the System of Document for this knowledge, because the legacy knowledge retailer was now not up to date.
Any downstream utilization of that knowledge, akin to experiences, additionally needed to be migrated to grow to be a part of or use the brand new
area service.
Stage 4 – Migrate area enterprise guidelines / logic to the brand new service(s)
At stage 4 enterprise logic was migrated into the brand new area providers (remodeling them from anemic “knowledge providers”
into true enterprise providers). The entrance finish remained unchanged, and was now utilizing a legacy facade which
redirected implementation to the brand new area service(s).